Secret detection is only the first step—true risk reduction comes from understanding context, validating exposure, and integrating remediation into existing workflows. Without these, detected secrets remain mere noise. This listicle explores how Vault Radar transforms detection into a measurable risk reduction process, covering correlation, webhooks, and cross-team accountability. Each point dives into a critical aspect of moving from discovery to control.
1. Detection Alone Isn't Enough
Surface-level secret scanning across code repositories, collaboration tools, and cloud environments reveals sprawl, but discovery does not automatically reduce risk. The initial detection is akin to a warning light—it signals a problem but doesn't diagnose its severity. In practice, security teams may identify hundreds of exposed secrets daily, yet without context, each finding remains ambiguous. The real challenge lies in determining whether a secret is still active, whether it’s already managed securely, and what the appropriate remediation path should be. Detection must be paired with analysis to move from visibility to action. Otherwise, teams risk drowning in alerts without measurable improvement in security posture. The goal is not just to find secrets but to understand their impact and prioritize responses effectively.
2. Context Is the Missing Ingredient
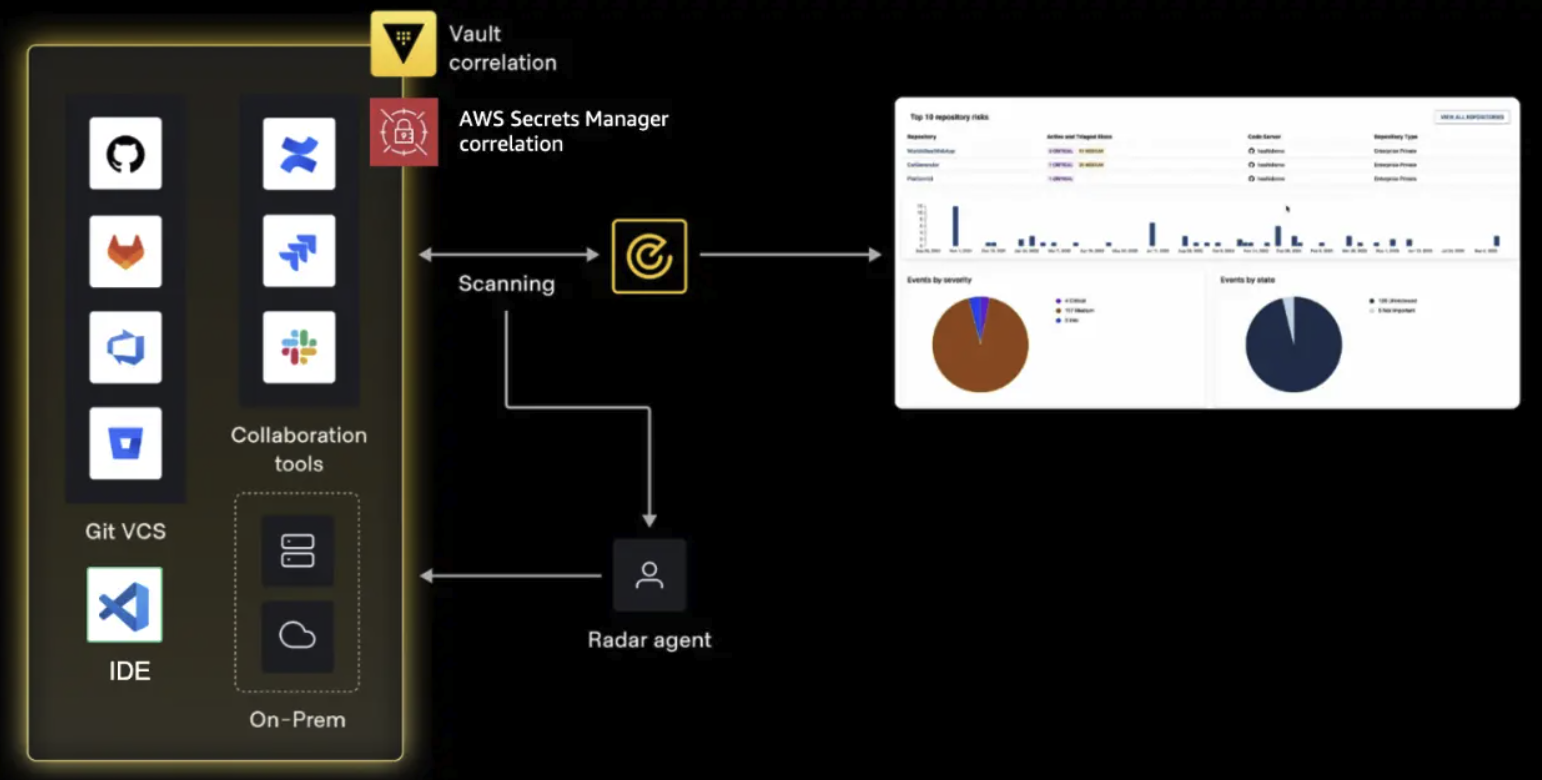
Once a secret is exposed, understanding its relevance is crucial. Is it a legacy credential stored in a script, or an active API key used in production? Validation steps like checking whether the secret is still active or if it references a non-existent resource save time and reduce false positives. Without this context, remediation efforts can be misdirected. For instance, rotating a deactivated key wastes developer cycles, while ignoring an active one leaves real risk unaddressed. Vault Radar introduces correlation mechanisms that automatically link findings to known secrets in systems like Vault or AWS Secrets Manager. This added layer transforms raw detection into actionable intelligence, enabling teams to quickly assess whether an exposure represents a genuine threat or a benign artifact.
3. Remediation Spans Multiple Teams
Secret remediation rarely falls under a single team’s purview. Security may identify the issue, but developers, platform engineers, and operations personnel often own the resolution. This cross-functional nature means that workflows must bridge different systems and responsibilities. A notification to the right owner may need to travel from a security dashboard to a ticketing system, then trigger a code fix or credential rotation. Without clear ownership and handoffs, secrets linger, increasing risk over time. Vault Radar addresses this by aligning detection with existing workflows—using webhooks to route findings to the appropriate channels. It also supports accountability by tracking progress from discovery to resolution, ensuring that every exposed secret has a defined owner and remediation path.
4. Vault Radar: The Bridge from Discovery to Control
Vault Radar is designed to help organizations build a mature remediation process around secret exposure. Its core function is not just detection but enabling a structured response: stronger context, better workflow alignment, and clearer accountability. The platform correlates findings with centralized secret stores, validates activity status, and triggers follow-ups automatically. This moves security teams from a reactive stance to a proactive governance model. Over time, Vault Radar measures progress, showing how many exposures are resolved, which teams are responding, and where gaps persist. The outcome is a demonstrable reduction in risk, tracked through metrics rather than hunches. By embedding remediation into existing processes, Vault Radar ensures that detection leads to action, not just alerts.
5. Correlation Provides Clearer Prioritization
Secret correlation links findings to known secrets in centralized systems like Vault or AWS Secrets Manager. This connection answers a critical question: Is this a managed secret that leaked, or an unmanaged secret created outside approved workflows? The distinction shapes the remediation path. For a managed secret, teams can rotate it within the existing vault with full lifecycle context. For an unmanaged secret, the exposure signals a governance gap—credential creation outside sanctioned processes. Correlation also reveals patterns over time, such as teams consistently storing secrets in code rather than vaults. By prioritizing findings based on correlation, organizations focus on the highest-risk exposures: unmanaged credentials that lack oversight and may indicate broader compliance violations.
6. Not All Secrets Are Equal
Every exposed secret doesn’t carry the same risk profile. A legacy password stored in a forgotten GitHub repo and a live AWS key in a production configuration file require vastly different responses. Correlation helps teams differentiate: a secret already managed in Vault may still need rotation if exposed, but the remediation is straightforward and tracked. Conversely, a secret not correlated with any vault points to credential sprawl outside sanctioned systems. Such findings demand urgent governance review. By categorizing secrets as managed but exposed versus unmanaged and exposed, teams can allocate resources efficiently. The former requires a tactical fix; the latter signals a strategic weakness in secret management policies. This distinction turns detection into a tool for continuous improvement, not just incident response.
7. Prioritize with Confidence Using Context
Armed with correlation data, teams can prioritize remediation with greater confidence. Instead of treating all findings as equal, they focus on those tied to active, unmanaged secrets that present immediate risk. Context from Vault Radar includes the secret’s age, last use, and associated permissions. For example, an API key with broad access to sensitive data that is not stored in a vault becomes a top priority. Meanwhile, a stale test credential can be deprioritized or auto-remediated. This risk-based approach aligns with security best practices and reduces alert fatigue. Over time, the organization can measure how many high-priority findings are resolved within target SLAs, providing a clear metric for risk reduction. Prioritization becomes data-driven, not subjective.
8. Webhooks Extend Remediation into Existing Workflows
Remediation doesn’t live in a single tool—it spans ticketing systems, CI/CD pipelines, chat platforms, and more. Vault Radar uses webhooks to push findings directly into the channels where teams already work. When a secret is detected, an automatic notification can fire to a Jira ticket, a Slack channel, or a PagerDuty escalation path. This ensures the right owner is alerted quickly, without requiring them to monitor yet another dashboard. Webhooks also trigger follow-up actions, such as creating a rotation request or starting a code review. By integrating into existing workflows, Vault Radar reduces friction and accelerates response times. The result: secrets get resolved faster, and the process feels natural to the teams involved.
9. Automate Remediation Where Possible
Beyond notification, automation can handle repetitive remediation steps. For secrets stored in vaults, Vault Radar can trigger automatic rotation when exposure is detected. For unmanaged secrets, it can alert administrators to enforce policy. Automation reduces manual toil and ensures consistent responses. For instance, a webhook might invoke a serverless function to revoke an exposed key immediately, then create a ticket for root cause analysis. This speeds up containment and limits blast radius. Over time, automated remediation patterns can be refined based on historical data, making the system smarter. The goal is to minimize human intervention for routine fixes while preserving human judgment for complex cases. Automation turns detection into near-real-time risk reduction.
10. Measure Progress Over Time
Risk reduction is not a one-time event; it requires ongoing measurement. Vault Radar provides dashboards and reports that track metrics like mean time to remediation (MTTR), number of unmanaged secrets, and correlation coverage. These indicators show whether the remediation process is improving. For example, a decreasing MTTR suggests that webhooks and automation are working. An increasing correlation rate means more secrets are being funneled into sanctioned vaults. Benchmarking these metrics over quarters demonstrates tangible risk reduction to stakeholders. It also identifies areas needing attention, such as teams with slow response times or high numbers of unmanaged secrets. Measurable progress shifts the conversation from theoretical safety to quantitative security posture, building trust with executive leadership.
Conclusion: From Detection to Reduction
Transforming secret detection into measurable risk reduction requires more than just scanning—it demands context, collaboration, and workflow integration. Vault Radar exemplifies this approach by correlating findings, automating notifications, and tracking progress. By following these ten principles, organizations can move from noisy alerts to a streamlined remediation pipeline that actively reduces risk over time. The key is to treat every exposed secret not as a failure but as an opportunity to strengthen governance and improve response practices. With the right tools and processes, secret detection becomes the foundation of a resilient security program.